Friday, 29 June 2012
Site to Site VPN, Remote VPN
A virtual private network (VPN) is a private network that interconnects remote (and often geographically separate) networks through primarily public communication infrastructures such as the Internet. VPNs provide security through tunneling protocols and security procedures such as encryption. For example, a VPN could be used to securely connect the branch offices of an organization to a head office network through the public Internet. A VPN can also be used to interconnect two similar-type networks over a dissimilar middle network for example, two IPv6 networks over an IPv4 network.
There are two main types of VPN: remote-access VPNs and Site-to-site VPNs.
Remote-access VPNs allow individual users to connect to a remote network such as roaming salespeople connecting to their company's intranet.
Site-to-site VPNs allow inter-connection of networks of multiple users for example, branch offices to the main company network. VPNs hence reduce costs as they eliminate the need for dedicated leased lines between networks, but instead use existing infrastructures to connect networks while adding a layer of security.
Intranet-based
It is when there are one or more remote locations that wish to join in a single private network, they can create an intranet VPN to connect each separate LAN to a single WAN.
Extranet-based
Extranet-based is like connecting LANs together. This extranet VPN allows different intranet to work together in a secure, shared network environment while preventing access to their separate intranets.
Client software
This software is require for people who wants to use VPN from their computers. This is needed to establish and maintain a connection to the VPN.The client software sets up the tunnelled connection to a NAS, which the user indicates by its Internet address. The software also manages the encryption required to keep the connection secure.
IPSec (ESP, AH, DES, MD5, SHA, DH)
Internet Protocol security (IPSec) is a framework of open standards for helping to ensure private, secure communications over Internet Protocol (IP) networks through the use of cryptographic security services. IPSec supports network-level data integrity, data confidentiality, data origin authentication, and replay protection. Because IPSec is integrated at the Internet layer (layer 3), it provides security for almost all protocols in the TCP/IP suite, and because IPSec is applied transparently to applications, there is no need to configure separate security for each application that uses TCP/IP.
The examples of IPsec are ESP, AH, DES, MD5, SHA, and DH.
IPSec helps provide defense-in-depth against:
• Network-based attacks from untrusted computers, attacks that can result in the denial-of-service of applications, services, or the network
• Data corruption
• Data theft
• User-credential theft
• Administrative control of servers, other computers, and the network.
Authentication Headers (AH)
AH provides connectionless integrity and data origin authentication for IP datagrams and provides protection against replay attacks.
Encapsulating Security Payloads (ESP)
ESP provide confidentiality, data-origin authentication, connectionless integrity, an anti-replay service (a form of partial sequence integrity), and limited traffic-flow confidentiality.
Data Encryption Standard(DES)
DES is a widely-used method of data encryption using a private (secret) key . DES applies a 56-bit key to each 64-bit block of data. The process can run in several modes and involves 16 rounds or operations.
Message Digest 5(MD5)
MD5 is a widely used cryptographic hash function with a 128-bit hash value. MD5 is widely used in security-related applications, and is also frequently used to check the integrity of files. MD5 value of file is considered to be a highly reliable fingerprint that can be used to verify the integrity of the file's contents. If as little as a single bit value in the file is modified, the MD5 value for the file will completely change. Forgery of a file in a way that causes MD5 to generate the same result as that for the original file is considered to be extremely difficult.
SHA
The Secure Hash Algorithm is one of a number of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S. Federal Information Processing Standard (FIPS):
Diffie-Hellman(DH)
The protocol has two system parameters p and g. They are both public and may be used by all the users in a system. Parameter p is a prime number and parameter g (usually called a generator) is an integer less than p, which is capable of generating every element from 1 to p-1 when multiplied by itself a certain number of times, modulo the prime p. However, it is vulnerable to a middleperson attack.
Security Associations (SA)
SA provides the bundle of algorithms and data that provide the parameters necessary to operate the AH and/or ESP operations. The Internet Security Association and Key Management Protocol (ISAKMP) provides a framework for authentication and key exchange, with actual authenticated keying material provided either by manual configuration with pre-shared keys, Internet Key Exchange (IKE and IKEv2), Kerberized Internet Negotiation of Keys (KINK), or IPSECKEY DNS records.
Public Key Infrastructure (Digital Cert)
PKI is a security architecture that has been
introduced to provide an increased level of confidence for exchanging
information over an increasingly insecure Internet. Public key
cryptography uses a pair of mathematically related cryptographic keys.
If one key is used to encrypt information, then only the related key can
decrypt that information.
A certificate is information referring to a public key, that has been digitally signed by a Certification Authority (CA). Certificates conforming to that standard include information about the published identity of the owner of the corresponding private key, the key length, the algorithm used, and associated hashing algorithm, dates of validity of the certificate and the actions the key can be used for. The CA takes responsibility for identifying (to a stated extent) the correctness of the identity of the person asking for a certificate to be issued, and ensures that the information contained within the certificate is correct and digitally signs it.
A certificate is information referring to a public key, that has been digitally signed by a Certification Authority (CA). Certificates conforming to that standard include information about the published identity of the owner of the corresponding private key, the key length, the algorithm used, and associated hashing algorithm, dates of validity of the certificate and the actions the key can be used for. The CA takes responsibility for identifying (to a stated extent) the correctness of the identity of the person asking for a certificate to be issued, and ensures that the information contained within the certificate is correct and digitally signs it.
Applications that use PKI:
- · Digital signatures
- · Smart card logon
- · Secure e-mail
- · Software code signing
- · IP Security (IPSec)
- · Software restriction policy
- · Internet authentication
- · Encrypting File System
- · PKI consist of a few components which are closely related together:
- · Certificate and CA management tools
- · Certification Authority (CA)
- · Registration Authority (RA)
- · Validation Authority (VA)
- · Attribute Authority (AA)
- · Attribute Certificates
- · Certificate Template
- · Digital Certificate
- · PKI enabled applications and services
Tuesday, 15 May 2012
Authentication, Authorization and Accounting
Authentication, authorization, and accounting (AAA) is a security architecture for distributed distributed systems, which enables control over which users are allowed access to which services, and how much of the resources they have used.
The process of authentication is based on each user having a unique set of criteria for gaining access. The AAA server compares a user's authentication credentials with other user credentials stored in a database. If the credentials match, the user is granted access to the network. If the credentials are at variance, authentication fails and network access is denied. Examples of types of credentials are passwords, one-time tokens, digital certificates, and phone numbers (calling/called).
After authentication, a user must gain authorization for doing certain tasks. After logging into a system, for instance, the user may try to issue commands. The authorization process determines whether the user has the authority to issue such commands. Simply put, authorization is the process of enforcing policies: determining what types or qualities of activities, resources, or services a user is permitted. Usually, authorization occurs within the context of authentication. Once you have authenticated a user, they may be authorized for different types of access or activity. Examples of types of service include, but are not limited to: IP address filtering, address assignment, route assignment, quality of Service/differential services, bandwidth control/traffic management, compulsory tunneling to a specific endpoint, and encryption.
The final process is accounting, which measures the resources a user consumes during access. This can include the amount of system time or the amount of data a user has sent and/or received during a session. Accounting is carried out by logging of session statistics and usage information and is used for authorization control, billing, trend analysis, resource utilization, and capacity planning activities.
Reference:
http://searchsecurity.techtarget.com/definition/authentication-authorization-and-accounting
http://en.wikipedia.org/wiki/AAA_protocol
Reference:
http://searchsecurity.techtarget.com/definition/authentication-authorization-and-accounting
http://en.wikipedia.org/wiki/AAA_protocol
Tuesday, 8 May 2012
Context-based access control
Context-based access control (CBAC) intelligently filters TCP and UDP packets based on application layer protocol session information that are not specifically denied by an ACL and can be used for intranets, extranets and internets. CBAC can be configured to permit specified TCP and UDP traffic through a firewall only when the connection is initiated from within the network needing protection.
With CBAC inspection rules, you can configure alerts and audit trail information on a per-application protocol basis. It generates real-time alerts and audit trails. Audit trails uses system log to track all the networking transaction. It can also mitigate Denial of Service (Dos) and detection which is essential for every computer.
CBAC inspects traffic that travels through the firewall to discover and manage state information for TCP and UDP sessions. This state information is used to create temporary openings in the firewall's access lists to allow return traffic and additional data connections for permissible sessions.

Every computer will have access to network, regarding work, surfing internet and so on. CBAC will check every packets that is in traffic. With CBAC, CBAC can examines the application-layer protocol information to learn about the state of TCP or UDP session. This ensures that our application are not downloading or allowing people to gain access to our computer through these applications.
With CBAC inspection rules, you can configure alerts and audit trail information on a per-application protocol basis. It generates real-time alerts and audit trails. Audit trails uses system log to track all the networking transaction. It can also mitigate Denial of Service (Dos) and detection which is essential for every computer.
CBAC inspects traffic that travels through the firewall to discover and manage state information for TCP and UDP sessions. This state information is used to create temporary openings in the firewall's access lists to allow return traffic and additional data connections for permissible sessions.

Every computer will have access to network, regarding work, surfing internet and so on. CBAC will check every packets that is in traffic. With CBAC, CBAC can examines the application-layer protocol information to learn about the state of TCP or UDP session. This ensures that our application are not downloading or allowing people to gain access to our computer through these applications.
Access list control
An access control list (ACL) is a table that tells a computer operating system which access rights each user has to a particular system object, such as a file directory or individual file. Each object has a security attribute that identifies its access control list. The list has an entry for each system user with access privileges. The most common privileges include the ability to read a file (or all the files in a directory), to write to the file or files, and to execute the file (if it is an executable file, or program).
.gif)
Different Operating System (OS) may use different Access Control List. When a user wants to initiate a specific action against a component item (for example, edit an article), the system checks the permission for this combination of user, item, and action. If it is allowed, then the user can proceed. Otherwise, the action is not allowed.
Allow: Allows this action for this level and group and for lower levels and child groups. This does not have any effect if a higher group or level is set to Deny or Allow. If a higher group or level is set to Deny, then this permission will always be denied. If a higher group or level is set to Allow, then this permission will already be allowed.
Deny: Denies this action for this level and group.
Access control list may include networking Access Control List (ACL), filesystem ACL and etc.
Reference:
http://en.wikipedia.org/wiki/Access_control_list
http://searchsoftwarequality.techtarget.com/definition/access-control-list
Sunday, 6 May 2012
Secure Perimeter Routers & Disable Services & Logging
The first line of defense against security threat is usually: Perimeter router, includes configuration of the perimeter. By disabling services and logging, network security can be more secure.
Some services which are rarely used like: CDP, finger, and TCP and UDP can be disable to secure the network even further. Hackers might make use of these service's security issue to try and gain unauthorized access into the network or get the network information.
Event logging is also important for security purpose, to reference is any security issues 'pop' out.
Interface status change, changes to system configuration, access list matches, events detected by the firewall, and intrusion detection features are some things that are log. Most routers are able to save system
logging information to a local RAM buffer.
There are different types of router configuration. Patches & Updates which means we have to stay updated to the latest patch and update. Protocols which means by using ingress and egress filtering, or screen ICMP traffic from internal network to counter protocol level attack. Administrative access which means deciding which interface and ports administration connection is allowed. Restricting access to the specific interfaces and ports, and encrypting them, having countermeasures against hijacking into these interfaces.
Some services which are rarely used like: CDP, finger, and TCP and UDP can be disable to secure the network even further. Hackers might make use of these service's security issue to try and gain unauthorized access into the network or get the network information.
Event logging is also important for security purpose, to reference is any security issues 'pop' out.
Interface status change, changes to system configuration, access list matches, events detected by the firewall, and intrusion detection features are some things that are log. Most routers are able to save system
logging information to a local RAM buffer.
There are different types of router configuration. Patches & Updates which means we have to stay updated to the latest patch and update. Protocols which means by using ingress and egress filtering, or screen ICMP traffic from internal network to counter protocol level attack. Administrative access which means deciding which interface and ports administration connection is allowed. Restricting access to the specific interfaces and ports, and encrypting them, having countermeasures against hijacking into these interfaces.
Common Threats to Router and Switch Physical &Mitigation
Basically, there are four common threats which are hardware threats, environmental threats, electrical threats and maintenance threats.
There are a few steps which can be taken for mitigation for hardware threats. The room must be locked with only authorized personnel allowed access. The room should not be accessible via a dropped ceiling, raised floor, window, ductwork, or any point of entry other than the secured access point.
If possible, use electronics access control with all entry attempts logged by security systems and monitored by security personnel. If possible, security personnel should monitor activity via security cameras with automatic recording.
Electrical threats include irregular fluctuations in voltage, such as brownouts and voltage spikes, Electrical threats, such as voltage spikes, insufficient supply voltage (brownouts), unconditioned power (noise), and total power loss can be mitigated by installing uninterruptible power supply (UPS) systems for mission-critical Cisco network devices, installing backup generator systems for mission-critical supplies, plannings for and initiate regular UPS or generator testing and maintenance procedures based on the manufacturer-suggested preventative maintenance schedule, installing redundant power supplies on critical devices, monitoring and alarm power-related parameters at the power supply and device levels.
Environment threats include very low and high temperature, moisture, electrostatic, and magnetic Interference. Threats like this should be mitigated by supplying the room with dependable temperature and humidity control systems. Always verify the recommended the recommended environmental parameters of the Cisco equipment with the supplied product documentation, removing any source of electrostatic and magnetic interference in the room. Equipping remotely monitor and alarm the environment parameters of the room would also ensure mitigation.
Maintenance threats include not having backup parts or components for critical network components, not labeling components and their cabling correctly Maintenance threats including poor handling of key electronic components, electrostatic discharge (ESD), lack of critical spares, poor cabling , poor labeling, and many more. Steps can be taken for mitigation such as label clearly all equipment cabling and secure the cabling to equipment racks to prevent accidental damage, disconnection, or incorrect termination, use cable runs, raceways, or both to traverse rack-to-ceiling or rack-to-rack connections, always follow ESD procedure when replacing or working with internal router and switch device components, maintaining a stock of critical spares for emergency use, logged off administrative interfaces when leaving a station, and use more locks on each door as no room is totally secure. When the intruders are insider secure room, nothing is left to stop them from connecting a terminal to the console port of the Cisco router or switch.
Thursday, 3 May 2012
Network / Port Address Translation
Inside local address (private) - the IP address assigned to a host on the inside network. The address is usually not an IP address assigned by the Network Information Center (NIC) or service provider. This address is likely to be an RFC 1918 private address.
Inside global address (public) - A legitimate IP address assigned by the NIC or service provider that represents one or more inside local IP addresses to the outside world.
Outside local address - The IP address of an outside host as it is known to the hosts in the inside network.
Outside global address - The IP address assigned to a host on the outside network. The owner of the host assigns this address.
Network Address Translation (NAT) is designed for IP address conservation. It enables private IP networks that use unregistered IP addresses to connect to the Internet. NAT operates on a router, usually connecting two networks together, and translates the private (not globally unique) addresses in the internal network into legal addresses, before packets are forwarded to another network.
As part of this capability, NAT can be configured to advertise only one address for the entire network to the outside world. This provides additional security by effectively hiding the entire internal network behind that address. NAT offers the dual functions of security and address conservation and is typically implemented in remote-access environments.
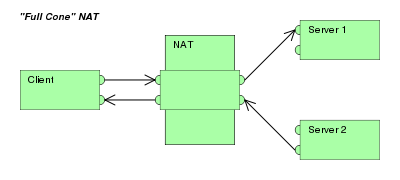
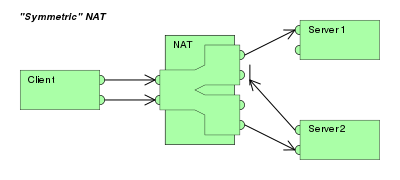
NAT also has different types of methods: Full-cone NAT, Restricted cone NAT, Port-restricted cone NAT and symmetric NAT. Full-cone NAT also known one-to-one NAT.


Port Address Translation (PAT) is also called porting, port overloading, port-level multiplexed NAT and single address NAT. During PAT, each computer on LAN is translated to the same IP address but with a different port assignment. PAT does not work alone. It always works with NAT as PAT only translates port and not the IP address.
Perimeter router, internal router and firewall
Perimeter router is a type of router which is used for the outside network
to connect to the internal network.
Internal network is used within the network.
Both do the same things the only exception is that they are used in different topology.
In every router topology, a firewall is needed to secure the network. The firewall allows the user to make certain rule to decide what type of traffic would be allowed in or out of the user's private network. Some firewall can restrict only certain IP address or domain names and some block certain type of traffic by the port they use.
Different organizations use different types of topology in their network.
For instance, a small business uses a standalone perimeter router topology as it doesn't require a lot of security in it's network. This topology, connects the untrusted network to the company's private network through perimeter router.
Another example is the perimeter router with integrated firewall. This is more commonly use in small/medium organizations for a better protection of the network than just only the router protecting the network, and have a better rate of data transfer.
One more example is the perimeter router, internal router and firewall topology. This topology used both the perimeter and internal router. The perimeter router would connect to the firewall which would connect to the internal router which connects the public network to the private network of the organization. Usually large/medium organizations use this topology for greater routing options, better performance and protection.
Internal network is used within the network.
Both do the same things the only exception is that they are used in different topology.
In every router topology, a firewall is needed to secure the network. The firewall allows the user to make certain rule to decide what type of traffic would be allowed in or out of the user's private network. Some firewall can restrict only certain IP address or domain names and some block certain type of traffic by the port they use.
Different organizations use different types of topology in their network.
For instance, a small business uses a standalone perimeter router topology as it doesn't require a lot of security in it's network. This topology, connects the untrusted network to the company's private network through perimeter router.
Another example is the perimeter router with integrated firewall. This is more commonly use in small/medium organizations for a better protection of the network than just only the router protecting the network, and have a better rate of data transfer.
One more example is the perimeter router, internal router and firewall topology. This topology used both the perimeter and internal router. The perimeter router would connect to the firewall which would connect to the internal router which connects the public network to the private network of the organization. Usually large/medium organizations use this topology for greater routing options, better performance and protection.
Friday, 27 April 2012
Security policy
Security policy is a set of rules which people who are given access to the organization's technology and information must follow in order for the assets to have confidentiality, integrity and availability.
Security policy is created to have a baseline of the organization security posture, set the framework for the security implementation, to set a behavioral code, determine the procedures and tools, define roles and communicate consensus, and handle security incidents.
There are two types of elements in security policy. Firstly, network design factors upon which security policies are based. Secondly, basic Internet threat vectors toward which security policies are written to mitigate.
As a continuous process of security policy, there is Network security which is done in four steps.
Firstly, secure, where there are security solutions being implemented to prevent unauthorized persons to access the assets. Authentication, encryption, firewall and vulnerability patching are some security solutions.
Secondly, monitor, where system auditing and real-time intrusion detection is used so that violations to the security policy will be detected. This step authenticate the security implementation of the 'secure' step.
Thirdly, test, this shows the effectiveness of the policy.
Last but not least, improve, where the information that was gathered from the 'test' and 'monitor' steps are use to make improvements to the security implemented.
Security policy is created to have a baseline of the organization security posture, set the framework for the security implementation, to set a behavioral code, determine the procedures and tools, define roles and communicate consensus, and handle security incidents.
There are two types of elements in security policy. Firstly, network design factors upon which security policies are based. Secondly, basic Internet threat vectors toward which security policies are written to mitigate.
As a continuous process of security policy, there is Network security which is done in four steps.
Firstly, secure, where there are security solutions being implemented to prevent unauthorized persons to access the assets. Authentication, encryption, firewall and vulnerability patching are some security solutions.
Secondly, monitor, where system auditing and real-time intrusion detection is used so that violations to the security policy will be detected. This step authenticate the security implementation of the 'secure' step.
Thirdly, test, this shows the effectiveness of the policy.
Last but not least, improve, where the information that was gathered from the 'test' and 'monitor' steps are use to make improvements to the security implemented.
Common Networking Attacks Threats and Solution
Network attack is also known as threat or any other attack that cause the network to be unable to access information in the network. Some Network security threats have three primary flaws: technology weakness, configuration weakness and policy weakness.
An example of network attack is Reconnaissance attack. This is used to gather information on a specific network. This may look harmless but the information the hacker gathered might be used in other attacks like Denial of Service (DoS) attack. This cannot be prevented entirely. IDSs at the network and host level can inform an admin when this attack occur.
Another example is Packet Sniffer. This software application is use in a network adapter card in promiscuous mode, capturing all network packets. This attack can only be mitigated, by example authentication, switched infrastructure, anti-sniffer tools and cryptography.
Another example is Application Layer Attack. This attack exploit popular weakness (example protocols that are intrinsic to an application or system), uses ports that firewall allows, and can never be entirely eliminate. This attack can only be reduced by: analyzing operating system and network log files, keeping the OS and application with the latest and up-to-date patch,etc.
One more example is Unauthorized access. Which means people who are not authorized get access into the private network. There are many kinds of attacks that can cause this, like: password attacks. This can be mitigated by having a more complex password and taking away the ability of hackers to have access into the network.
An example of network attack is Reconnaissance attack. This is used to gather information on a specific network. This may look harmless but the information the hacker gathered might be used in other attacks like Denial of Service (DoS) attack. This cannot be prevented entirely. IDSs at the network and host level can inform an admin when this attack occur.
Another example is Packet Sniffer. This software application is use in a network adapter card in promiscuous mode, capturing all network packets. This attack can only be mitigated, by example authentication, switched infrastructure, anti-sniffer tools and cryptography.
Another example is Application Layer Attack. This attack exploit popular weakness (example protocols that are intrinsic to an application or system), uses ports that firewall allows, and can never be entirely eliminate. This attack can only be reduced by: analyzing operating system and network log files, keeping the OS and application with the latest and up-to-date patch,etc.
One more example is Unauthorized access. Which means people who are not authorized get access into the private network. There are many kinds of attacks that can cause this, like: password attacks. This can be mitigated by having a more complex password and taking away the ability of hackers to have access into the network.
Subscribe to:
Comments (Atom)